Table of Contents

We’re not talking hackers in their mom’s basement. These groups have dedicated teams for Account Creation, Transacting, and Withdrawal. A high-tech, assembly line of fraud that drained 7-figures-a-month from a major platform before they were stopped.
Welcome to GeoComply’s Fraud Files—true fraud stories from the industry’s front lines.
GeoComply’s Risk Research team travelled into far corners of the dark web to gather the intel about today’s case.
Join us behind the scenes as we talk to Matt Boland, GeoComply’s Senior Manager of Fraud and Risk, to explore how a fraud ring scaled their multi-million dollar promo abuse, stolen identity, and chargeback attack—and how one organization shut it down, preventing over $5 million USD in losses.
The attack launched using teleportation devices
It begins with location spoofing. And we’re not talking about hiding IP via VPN or proxy.
Ever heard of a faraday cage?
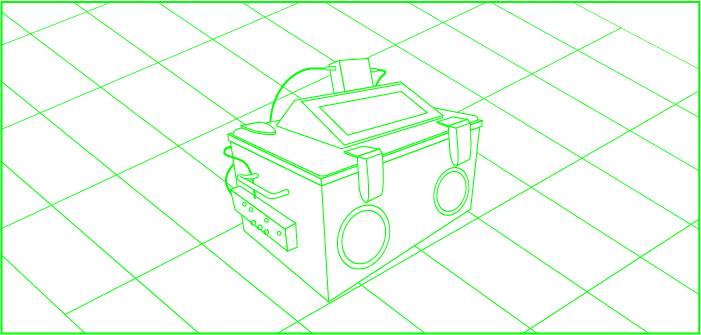 Rendering of faraday cage setup used to isolate devices from GPS/Wi-Fi/cell signals.
Rendering of faraday cage setup used to isolate devices from GPS/Wi-Fi/cell signals.
For most, it’s something you’d find in a physics textbook or a hospital MRI room. An enclosure, like a big metal box, that blocks external electromagnetic fields. For this gang, it’s a ~$100K ticket to anywhere:
- They put devices inside the cage
- External signals (GPS, Wi-Fi, cell towers) are blocked, creating a location “dead zone”
- They use Wi-Fi injection to “teleport” into a local Wi-Fi point
- Because the cage blocks all other signals, the activity registers as local
TL;DR that transaction that’s tied to your neighbourhood Starbucks could be coming from anywhere.
How did this slip through?
“Standard fraud tools (and most identity checks) rely heavily on IP address as a proxy for location. An IP tells you roughly where a device’s internet connection originates, which is useful but limited. It can’t tell you whether the location is real. And IP can be easily circumnavigated by using a VPN or proxy,” says Matt.
To combat this, some organizations have fraud controls that go beyond IP, using corroborated GPS, Wi-Fi, and cell tower signals to pinpoint a user’s precise location.
A faraday cage defeats this entirely.
“By stripping a device of its real-world signals and injecting a chosen Wi-Fi point, the device looks indistinguishable from a genuine local user,” says Matt. “There’s no cell tower to reference. No GPS to detect. From the outside, it registers as a perfectly normal transaction from a perfectly normal location.”
Unless you know what else to look for.
“GeoComply’s ML models can detect signs of location spoofing by looking at device and behavioural signals that are consistent with faraday cage use. So, while the Wi-Fi point might look like a legitimate neighbourhood Starbucks, there are red flags surrounding the activity that point to advanced spoofing,” Matt says.
But we’re getting ahead of ourselves. Let’s head back behind enemy lines.
Next, they slipped through KYC
 Deepfakes, synthetic IDs, and stolen credentials are either bought in batches on the dark web or created using AI
Deepfakes, synthetic IDs, and stolen credentials are either bought in batches on the dark web or created using AI
With location convincingly spoofed, the operation moved to account creation. The tools of the trade: deepfakes, synthetic IDs, and stolen credentials, sourced in bulk from the dark web or generated using AI.
With location covered, they:
- Created accounts on jailbroken and reset devices
- Used synthetic, stolen, and deepfake IDs to sign up at scale
- Made small deposits via stolen payment methods
Each account was passed down the assembly line from creation to deposit to withdrawal.
How did this slip through?
“This is why basic IP checks and document-only identity verification can look completely clean,” says Matt.
“A synthetic ID doesn’t trigger a document alert. A jailbroken device doesn’t wave a flag. A spoofed Wi-Fi point doesn’t look suspicious. Each signal, in isolation, passes. It’s only when you layer location, device, and behavioural intelligence together that the pattern becomes visible.”
The giveaway: In-platform activity
In this case, the weak point wasn’t registration. It was the behaviour within the platform.
The strategy is to remain active just enough to qualify for the org’s promotion. Often these are rapid transactions. Fast movement, quick cash.
The organization triggered location and device intelligence checks after suspicious patterns appeared.
That’s when the connections surfaced:
- Activity was clustered at multi-accounting hotspots…
- On devices that showed signs of manipulation…
- At Wi-Fi points that were being actively spoofed.
How did they catch this?
Clustered activity raised the red flag—so what does “clustered activity” really mean?
In fraud detection, clustering is what happens when you look at signals together rather than individually. A single account transacting quickly isn’t suspicious.
But a hundred accounts transacting quickly, all originating from overlapping device IDs, at the same spoofed Wi-Fi point, at the same time? Well, that’s a pattern.
“This is where behavioural intelligence earns its place in the stack. Location and device signals tell you where accounts are and what they’re running on. Behavioural signals tell you how they’re acting. When all three converge, the picture becomes very hard to argue with,” says Matt.
The real win: Stop it while it’s hot
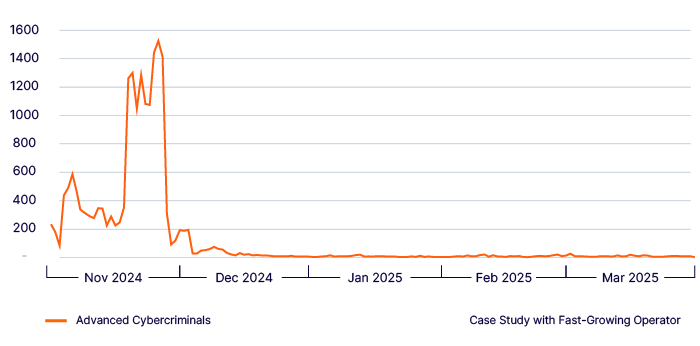
GeoComply’s ML models can detect and flag this activity within 3.8 minutes, so the organization can act before the damage racks up. Once this org set up an automated response:
- 96% of spoofers were blocked before withdrawal
- 68% were stopped before deposit
- Over $5 million was prevented or reclaimed in 2 months
But the story doesn’t end here.
Fraud on tour
Here’s the part that keeps fraud and risk teams up at night: these groups don’t stop. They adapt.
When the attack stopped working at this platform, the group moved on. They targeted another. The same defences were deployed. They moved on again.
One platform attributed 9,300 “new” accounts to this scheme, at an average cost of $200 USD per account. That’s over $1.86 million in direct losses, before accounting for chargebacks from the stolen cards, wasted marketing spend on the promotions, and the investigative hours burned tracking it down…
“This is what makes full-stack fraud rings genuinely dangerous. They’re not opportunistic. They’re systematic. They have budgets, tooling, and the patience to probe for gaps.
When one door closes, they find another. The platforms that fare best aren’t the ones who react fastest—they’re the ones who’ve built defences that make the attack not worth running in the first place,” says Matt.
How to catch a full-stack cybercriminal
GeoComply’s ML models picked up on synthetic location signals that slipped past identity checks and other fraud controls. By layering in device and behavioural intelligence alongside precise location, platforms are able to pinpoint this activity and stop it mid-flight.
The insight here isn’t just that these signals caught the fraud. It’s that catching it at onboarding*, before the assembly line gets going, is what shortens the window dramatically.
“Every stage the fraud ring completes costs money. Stop it at account creation and you’ve avoided the deposit, the transaction, the withdrawal, and the chargeback. With the right signals, it can be that simple,” says Matt.
If you want to learn more about how location, device, and behavioural intelligence can help defend your platform from full-stack fraud rings, book a demo.
*P.S. Operators like Dabble UK are doing just that—adding a location check and fraud detection helped them bust a 2,000-strong device emulator farm in London.
Madeleine Ritzker | Fraud Journalist, GeoComply
Madeleine Ritzker covers fraud intelligence for GeoComply, mining the hard work of the industry’s risk and fraud teams and translating it into stories that reveal what’s actually happening on the digital front lines. Fraud Files is your way to keep up with the latest tricks and trends sweeping through the darkest corners of the web.
Matt Boland | Senior Manager of Fraud and Risk, GeoComply
Matt leads the Fraud and Risk Management (FARM) team, GeoComply’s dedicated fraud and risk partnership unit, sitting at the intersection of client relationships, fraud expertise, and machine learning capabilities. The FARM team translates real-world fraud patterns into better tools and better outcomes for clients, working directly alongside them to tackle emerging threats as they happen, not after the fact.