Table of Contents

Unique devices. Unrelated users. How did Dabble UK connect 250+ bonus abuse accounts back to one house?
Welcome to GeoComply’s Fraud Files—true fraud stories from the industry’s front lines.
Today, we’re travelling to Preston, England, where the fraud team pinned a surge of bonus abuse to one multi-accounting hotspot.
We’re joined by Hila Popal, the GeoComply Fraud and Risk Analyst who partnered with the Dabble UK team to surface the attack and shut it down.
The setup: That promo must be working, right?
 Basic, silo’d signals would have left Dabble in the dark. Precise location and device intelligence linked seemingly unique devices to one address.
Basic, silo’d signals would have left Dabble in the dark. Precise location and device intelligence linked seemingly unique devices to one address.
Dabble, an iGaming platform, entered the competitive UK market with a strong rollout of enticing promotions. And Preston seemed to love it. An influx of new registrations—random player names, different usernames. Just what you want, right?
Not quite.
Multi-accounting: The problem with looking good on paper
(Spoiler alert. It was an aggressive multi-accounting fraud ring.)
Without the right signals, the fraud team would have been left chasing individual cases. Each account looked “unique”: fresh username, new device ID, no obvious links.
You don’t need us to tell you that this game of whack-a-mole becomes a slow, manual slog. And the abuse can scale long before it’s stopped.
“Multi-accounting is designed to fool basic tools. And it does,” Hila says. “But device-sharing signals, account-sharing patterns, and device reset detection tell a different story. Once you can see that layer, the ring unravels fast.”
The Dabble difference
Dabble had an edge.
They’d layered new tools into their identity stack: GeoComply’s location, device and behavioural intelligence. Ground truth signals that work together to paint the invisible lines between those new usernames and devices.
“Because Dabble had gathered these signals right at registration, we had powerful data to work with right from the start. Rather than retroactively putting the pieces together, this gave us a clear picture of how these users, devices, and locations were related, in real-time,” Hila explains.
“Because Dabble had gathered these signals right at registration, we had powerful data to work with right from the start. Rather than retroactively putting the pieces together, this gave us a clear picture of how these users, devices, and locations were related, in real-time,” Hila explains.
This surfaced hidden connections between seemingly random players.
The signals: That don’t imPreston me much
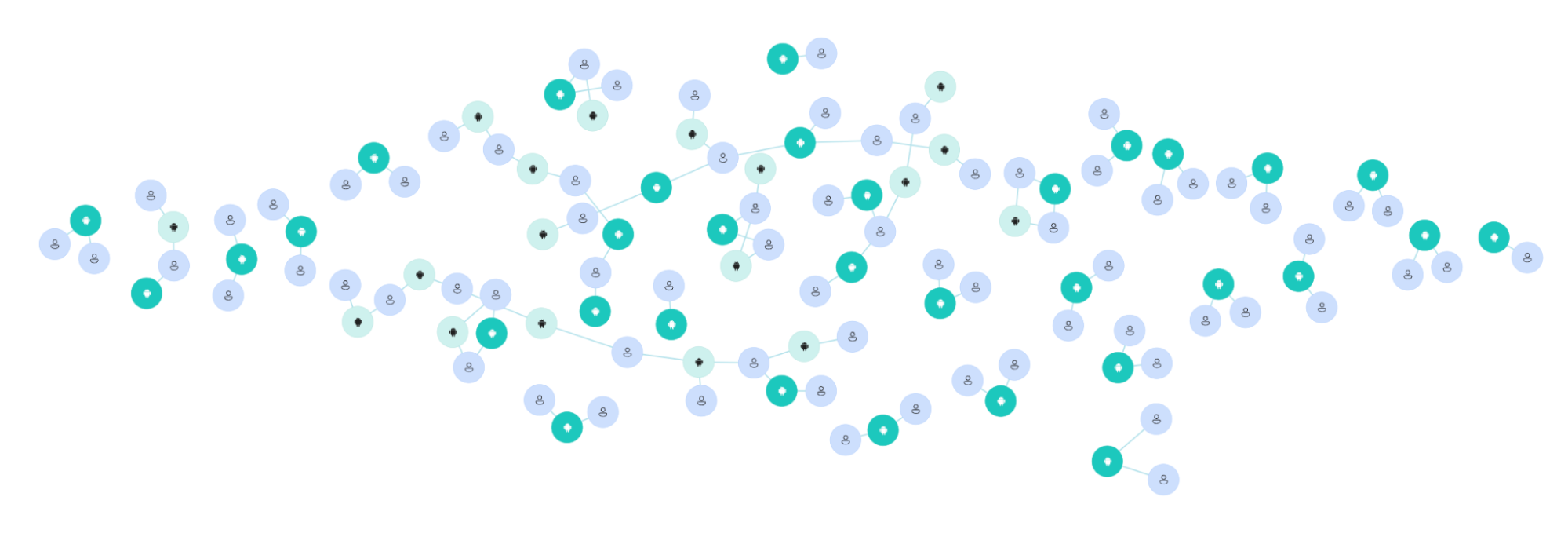 Map of connected users and devices, all located at one Preston address
Map of connected users and devices, all located at one Preston address
Using precise location coordinates—drawn from a combination of GPS, Wi-Fi, IP, and cell tower signals—Dabble traced over 250 of these accounts to a single residential address.
They detected:
- Two devices repeatedly reset to create “new” device IDs
- Accounts created using suspected stolen or synthetic identities
- Activity lasting just long enough to qualify for and redeem the promotion
- Before the device was reset, and the cycle repeated
GeoComply linked this one Preston location to over 280 new device UUIDs active across 255 users. Just one cluster of this activity—8 linked devices and users—caused an estimated £1,000 in bonus abuse damage alone.
“That’s one cluster, at one address, in one city. It doesn’t account for the investigation time that would have been burnt, or the wasted marketing spend,” Hila says. “We also often see chargebacks crop up later down the line, when victims have realized their payment details have been compromised and exploited. The earlier you spot it, the less damage.”
Precise location: The smoking gun
This is where basic, IP-based tools hit their ceiling. From an IP address alone, you’re working with a location radius of roughly 100km.
That’s enough to tell you someone’s probably in Greater Manchester (unless they’re using a VPN or proxy). It’s not enough to tell you they’re in the same living room as the last 249 accounts that were approved.
“Simply put, Dabble did two key things really well: they gathered device, location, and behavioural intelligence early in the journey. And then they mixed those signals together,” says Hila. “This allowed them to clearly see clusters and connections that would have otherwise been invisible.”
The shutdown: Pinning down promo abuse
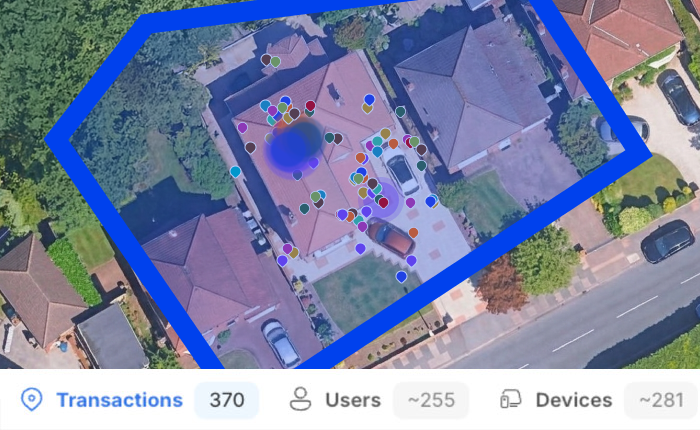 Dabble’s perimeter alert setup in GeoComply’s platform
Dabble’s perimeter alert setup in GeoComply’s platform
Once the cluster was confirmed, Dabble worked with GeoComply to set up a real-time perimeter alert at the Preston location, with proactive monitoring feeding back directly into their KYC process.
This means they can instantly detect and respond to new activity with a step-up challenge, stopping fraud attempts without disrupting legitimate players who happen to live nearby.
Anyone who has ever collaborated with the Product team knows that last part matters.
“The false positive problem is one of the biggest operational tensions in fraud prevention: block too aggressively and you start turning away real customers. Precise location lets operators draw finer lines, targeting suspicious activity at a specific address rather than flagging an entire postcode,” Hila says.
Why precise location changes the game
If you’re still relying on IP-based geolocation, here’s the part worth getting nerdy about.
IP location works by mapping an internet address to a known physical area. The problem is that IP addresses are assigned to ISPs (internet service providers), not individual homes. And an ISP can serve thousands of customers across a wide region.
The result is a location estimate that’s often accurate to a city (up to 100km or 60 miles in diameter). Sometimes it’s a neighbourhood. But it’s rarely a street. Add a VPN or proxy into the mix, and that already-fuzzy signal disappears entirely.
Precise location works differently. By combining GPS, Wi-Fi access point data, cell tower triangulation, and IP together, it’s possible to establish where a device actually is—not where its internet provider happens to be. That’s the difference between “somewhere in Preston” and “this address on this street.”
“Even better, we can see when someone is trying to hide their location or device fingerprint. That’s the difference between a normal customer and someone with malicious intent,” Hila says.
For fighting fraud, that difference is everything. Device resets can generate new IDs. Synthetic profiles can pass document checks. But, with GeoComply on the other side, fraudsters can’t fake the location of a physical device. And if they try, you’re the first to know.
The TL;DR tricks of the trade
Fraudsters scale promo abuse through a reliable playbook: device resets, stolen or synthetic IDs, and coordinated account farming. The accounts look different, but the pattern doesn’t—if you have the right signals to see it.
Dabble did. What made the difference:
- Location intelligence beyond basic IP—pinpointing real-world device location, not ISP geography
- Real-time device and multi-account detection—surfacing connections between “unique” accounts the moment they appear
- High-risk location and multiple-user flags—delivered directly into case workflows, cutting manual review time
Hila sums it up: “device resets and synthetic IDs are table stakes for these groups. The accounts look different by design. What Dabble had was the ability to see through that, not because any one signal gave it away, but because the combination of location, device, and behaviour made the pattern impossible to ignore.”
Want to see how organizations are catching multi-accounting and promo abuse faster, and cutting manual review workload while they’re at it? Talk to our Fraud and Risk Management team.
Madeleine Ritzker | Fraud Journalist, GeoComply
Madeleine Ritzker covers fraud intelligence for GeoComply, mining the hard work of the industry’s risk and fraud teams and translating it into stories that reveal what’s actually happening on the digital front lines. Fraud Files is your way to keep up with the latest tricks and trends sweeping through the darkest corners of the web.
Hila Popal | Fraud and Risk Analyst, GeoComply
Hila partners directly with organizations to tackle fraud on the front lines. Her work spans threat analysis, custom rule development, and ML model tuning, translating real-world fraud patterns into practical defences built around each platform’s specific risk profile.
Note: Case images have been anonymised to protect personal data. All details shown are reflective of the true investigation.