Table of Contents

~2,000 new users in London doesn’t sound particularly suspicious. That is, until Dabble UK traced them all back to a posh park in Mayfair.
Welcome to GeoComply’s Fraud Files—true fraud stories from the iGaming front lines.
Today, we’re traveling to Berkeley Square, former stomping ground of Prime Ministers, Countesses, and the co-founder of Rolls-Royce. Also a hotspot for fraud, where a device emulator farm was attempting to harvest bonuses.
We’re joined by GeoComply’s Hila Popal, the Fraud and Risk Analyst who helped Dabble crack the case.
The setup: That promo must be working, right?
 IP alone is a haystack full of 9M Londoners. With precise location, Dabble pinpointed the activity to one park.
IP alone is a haystack full of 9M Londoners. With precise location, Dabble pinpointed the activity to one park.
Dabble hit the UK market running with a rollout of competitive promotions. On the surface, new signups in London looked like a good sign. Unique players, unique devices, seemingly healthy activity.
But Dabble was looking deeper.
Having layered GeoComply’s device and location intelligence into their KYC process, they had a high-res view of not only who was behind account creation, but where it was coming from.
That was the tell.
Why gathering signals early matters
This is the part that often gets overlooked. Most fraud teams focus their detection efforts on in-platform behaviour: transactions, suspicious patterns, complaints from legitimate users. By then, the fraud has already had time to scale.
“The earlier you gather intelligence, the more powerful it is,” Hila says. “Dabble wasn’t retroactively trying to piece together a pattern because we had ground truth data from the very first interaction. Every subsequent action was already connected to a device, a location, and history. Looking at those signals together (and seeing which ones were being spoofed) is what led them to bust this ring.”
Collecting these signals at KYC isn’t just about catching fraud at the door. It’s about building a high-resolution picture of user behaviour from the moment they arrive. Then, when something looks off, the evidence is already there.
London calling. And calling. And calling…
 Advanced device intelligence picked up on emulator use and attempted location spoofing.
Advanced device intelligence picked up on emulator use and attempted location spoofing.
Armed with device signals and precise location intelligence gathered at registration, Dabble detected:
- Devices repeatedly reset to generate “new” device IDs
- Virtual machines and emulators used to mask true location
- New profiles created, funded, and played just long enough to qualify for the promotion
- Devices reset—and the cycle repeated
Almost 2,000 of these seemingly individual users and devices were connected and geolocated back to Berkeley Square.
The magic of mixing signals together
On its own, a device reset is a flag. An emulator is a flag. An account that qualifies for a bonus and goes quiet is a flag. But individually, each of these could have an innocent explanation.
“The real insight comes from combining signals,” Hila says. “Location tells you where someone is or whether they’re trying to hide where they are. Device intelligence tells you what they’re using and whether it’s been tampered with. Behavioural signals tell you how they’re acting. When you layer all three together, the picture becomes very hard to misread.”
What looked like 2,000 individual users became one coordinated operation using emulators to “teleport” to one location. And that connection was only visible because the signals were working together.
This is what high-resolution risk looks like in practice. Not a single smoking gun, but a constellation of signals that, combined, make the pattern undeniable.
The shutdown: Setting up a neighbourhood watch
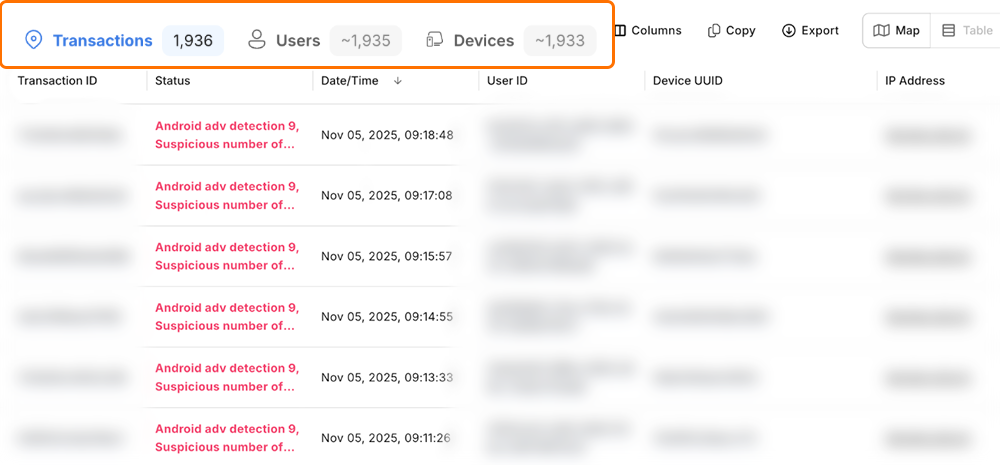
 Dabble’s perimeter alert setup in GeoComply’s platform
Dabble’s perimeter alert setup in GeoComply’s platform
With this evidence, Dabble quickly blocked the devices and shut down the attack.
They worked with GeoComply to set up a perimeter alert, with monitoring that flags suspicious activity in real-time.
This allows them to react without impacting legitimate players who happen to be strolling through Berkeley Square.
Why continuous monitoring changes the equation
Static fraud rules have a well-known weakness: fraudsters figure them out and route around them. A rule that blocks based on a known device ID is useless the moment that device is reset. A rule based on a flagged IP address fails the moment a VPN is switched on.
“Continuous monitoring throughout the customer journey closes that gap,” Hila says. “We’re not just checking at registration and walking away. We’re watching how risk evolves in real time. So if a device that looked clean at signup starts behaving suspiciously during a session, we catch it while it’s still active in the platform.”
The power of device + location + behaviour
From an IP-only view, London has over 9 million potential suspects.
“Dabble’s edge was the combination of location, device, and behavioural intelligence,” Hila says. “It saved their team from investigating ~2,000 individual users and shone a light on a glaring fraud hotspot. From there, they could pinpoint bad actors without impacting good players.”
That last point matters as much as the detection itself.
Fraud prevention that creates friction for legitimate users has its own cost in conversion, in trust, in customer lifetime value. Corroborating these signals makes it possible to draw finer lines: targeting suspicious activity at a specific address in Berkeley Square rather than flagging every account registered anywhere in Mayfair.
“This is one of the biggest misconceptions about fraud controls,” Hila adds. “People assume that more aggressive detection means more friction for real customers. It doesn’t have to. The more precise your signals, the more precise your response can be, so you stop the fraud ring, not the person who lives down the road.”
The TL;DR tricks of the trade
Device emulator farms scale bonus abuse through a reliable playbook: virtual machines, device resets, and coordinated account farming. The accounts look unique. But the signals don’t lie.
What made the difference for Dabble:
- Ground truth signals gathered at KYC: building a real-time picture from the first interaction, not retroactively
- Location and device intelligence combined: surfacing the connections between “unique” accounts that no single signal could reveal alone
- Continuous monitoring throughout the journey: catching risk while it’s still active, not after the damage is done
- Precise, surgical responses: stopping bad actors at a specific address without creating friction for legitimate users nearby
To learn more about how you can get ahead of the fraud ring that might be hiding in your local park, book a chat with our fraud experts.
Madeleine Ritzker | Fraud Journalist, GeoComply
Madeleine Ritzker covers fraud intelligence for GeoComply, mining the hard work of the industry’s risk and fraud teams and translating it into stories that reveal what’s actually happening on the digital front lines. Fraud Files is your way to keep up with the latest tricks and trends sweeping through the darkest corners of the web.
Hila Popal | Fraud and Risk Analyst, GeoComply
Hila partners directly with organizations to tackle fraud on the front lines. Her work spans threat analysis, custom rule development, and ML model tuning, translating real-world fraud patterns into practical defences built around each platform’s specific risk profile.
Note: Images in this article have been modified to protect personally identifiable information, but remain representative of the real case details.